This content has moved to http://oalabs.openanalysis.net/2013/11/19/screensaver-malware-using-scr-executables/
Remember way back in 2006 when custom screen savers were the new hotness and everyone was googling "free screensavers" and getting infected with trojaned slideshows of majestic wildlife? Well it seems screensaver malware has been re-invented in a clever new way and is being used to infect victims as part of a large e-mail trojan distribution campaign.
If you are reading this there is a good chance that you are trying to figure out why you are staring at an efax attachment that contains a screensaver (.scr) file. In order to understand this we will need to dive into the internals of windows file associations.
Background - Windows File Associations
Windows uses the file extension (the part of the file after the last . ) to determine which program should be used to open the file. This is mapped in the HKEY_CLASSES_ROOT registry hive. In the hive there are a bunch of file extension keys.The value of these keys maps to a second key in the same hive which describes which how the file should be opened (/shell/open/command).
In the case of a few special files instead of being opened by another program there is a %1 in the key value that indicates the file should be executed itself. As you can see screen savers (.scr) are one such file. This means that any time you double click an .scr file you are really just executing it or to put it in even simpler terms .scr is just another extension for an executable (.exe).
The Malware Threat
It seems an ongoing e-mail trojan distribution campaign that had been using zipped .exe attachments has re-tooled and are now using zipped .scr attachments. The campaign seems to favour spoofing eFax emails with a spoofed address and a fairly decent replication of a real eFax e-mail.
Attached is a .zip file that contains the .scr file. As you can see on a default Windows7 system the file extensions are not visible and thanks to a pdf icon in the .scr file it does a good job of mimicking a real eFax PDF.

If we take a close look at the efax .scr file we can see that it is really nothing more than an executable with a pdf icon.
As we can see VirusTotal definitely identifies the .scr as a malicious file and malwr has a decent profile of its malicious behaviour.
Detection
So, why go to all the trouble of renaming the .exe malware to .scr? At first I suspected that this was part of the social engineering aspect of the e-mail; an attempt to make the file less suspicious to the victim. This may indeed be part of the reason for the renaming but, as noted above, file extensions are not visible on a default Windows7 install so most users will never see the extension. Instead I suspect the more plausible explanation for the rename is to avoid e-mail filter detection (and possibly some network antivirus detection). Some older/lower end/poorly configure IPS/IDS and e-mail filtering technology does not examine the full file contents and only uses the file extension to determine if an attachment is suspicious or not. This is especially true of zipped files given the overhead/bandwidth required to unzip and then inspect files.
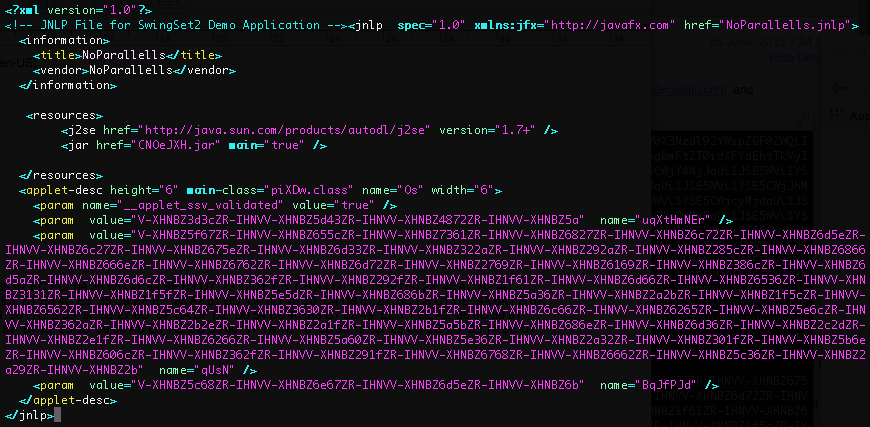
Whatever the reason, if you have IPS/IDS or e-mail filters that are just using file extensions in zip files to evaluate threats you will want to add .scr to the list of suspicious files. In fact I used a little powershell magic to search the HKEY_CLASSES_ROOT registry hive for all file extensions that are treated like executable files.
HKEY_CLASSES_ROOT\.bat = batfile HKEY_CLASSES_ROOT\batfile\shell\open\command = "%1" %* HKEY_CLASSES_ROOT\.cmd = cmdfile HKEY_CLASSES_ROOT\cmdfile\shell\open\command = "%1" %* HKEY_CLASSES_ROOT\.com = comfile HKEY_CLASSES_ROOT\comfile\shell\open\command = "%1" %* HKEY_CLASSES_ROOT\.exe = exefile HKEY_CLASSES_ROOT\exefile\shell\open\command = "%1" %* HKEY_CLASSES_ROOT\.pif = piffile HKEY_CLASSES_ROOT\piffile\shell\open\command = "%1" %* HKEY_CLASSES_ROOT\.scr = scrfile HKEY_CLASSES_ROOT\scrfile\shell\open\command = "%1" /SBased on these results you should be detecting .bat .cmd .com .exe .pif and .scr files in .zip e-mail attachments as potentially malicious. In fact, if we look though the most recent efax submission to malwr.com it looks like another file extension .pif is already been used by the malware campaign.
pdf_efax_4298299310.pif pdf_efax_6785462001.scr efax_9057733019_pdf.zip efax_9057733019_pdf.exe efax_9057733019_pdf.scr pdf_efax_9057733019.scr pdf_efax_9057733000.scr